Enterprise Infrastructure Solutions (EIS) transition
The transition to Enterprise Infrastructure Solutions (EIS) is one critical path for agencies to evolve to more modernized and secure IT infrastructures and away from legacy technologies that are vulnerable to security risks — a high priority for this Administration. With the President’s Executive Order on Improving the Nation’s Cybersecurity, it’s important to remember that the transition to EIS is not about shutting down expiring contracts; it’s ultimately about the safety, security, and sustainability of the federal government’s IT infrastructure.
The most recent EIS transition milestone came and went on March 31, when agencies were expected to have disconnected at least 50 percent of their services from the expiring Networx, Washington Interagency Telecommunications System (WITS) 3, and Local Service contracts.
While the data illustrates agencies are making progress, with 55% of the federal government’s inventory remaining to be disconnected, there is still much work to be done. Therefore, we urge our agency partners to take A.I.M. at EIS:
- Assess their status and accelerate their progress
- Disconnect & transition their Inventory
- Mitigate risk to ensure mission operations continue
Assessing status and accelerating progress
Less than two years remain before the Networx, WITS 3, and Local Service contracts expire on May 31, 2023. Though the September 30, 2022 deadline for 100% disconnect from expiring contracts is a little over 15 months away, we want to remind agencies that a lack of transition progress could result in service disconnection much sooner. Please assess your progress against several important dates that are outlined in the revised Project Plan for Closeout of Transition and accelerate actions accordingly:
- June 30, 2021 – Agencies that are not transitioning to EIS will have services disconnected. On this date, agencies for whom GSA has provided a report for a price-only fair opportunity decision, but have yet to award the task order, will also be disconnected.
- August 31, 2021 – Agencies that have not awarded any EIS task orders for their solicitations will be disconnected.
- September 30, 2021 – Agencies that have not awarded EIS task orders for all their solicitations will be disconnected.
- October 1, 2021 – GSA will no longer accept or process any exception requests for the expiring contracts (Networx, WITS 3, and Local Service Agreements). All new services should be ordered from the EIS contracts or other viable contracts.
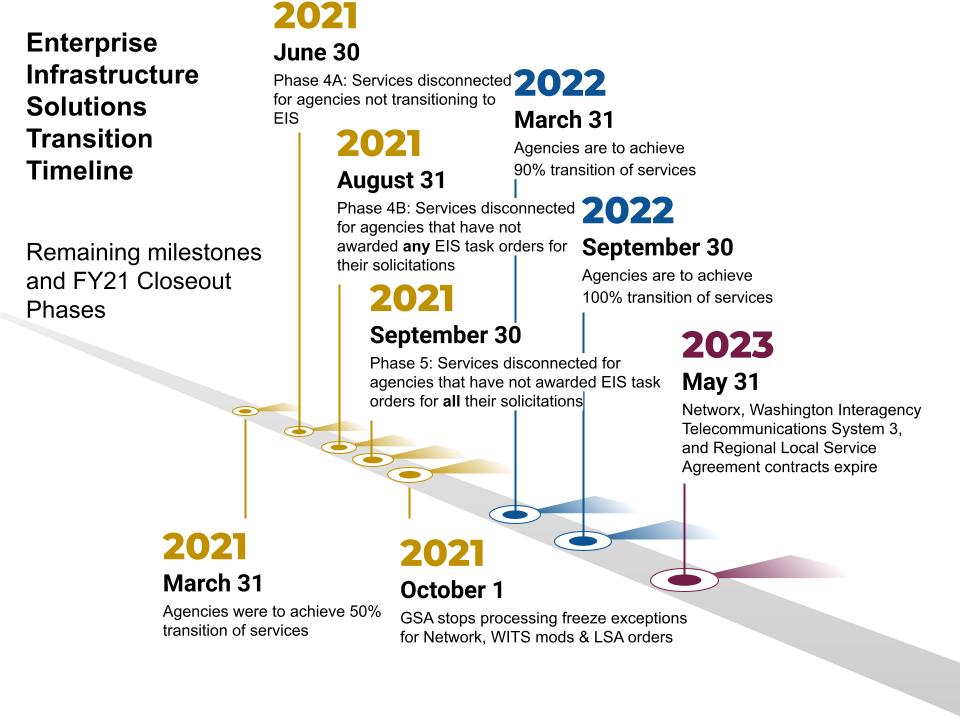
The next major milestone for EIS transition is on March 31, 2022, which calls for 90% of services disconnected from expiring contracts. With less than 12 months to go, we urge agencies to accelerate progress, so as not to fall further behind.
Inventory: enhanced focus on disconnecting and transitioning inventory to EIS
Government-wide, we are behind the EIS curve. 11 of 17 large agencies and 15 of 25 medium-size agencies have yet to disconnect even 50 percent of their services as of March 31, 2021. Ultimately, missing transition milestones and continued reliance on expiring contracts risks disruption of critical services delivered to the public.
Mitigating risk to ensure mission operations continue
The more agencies fall behind the established milestones, the greater the risk to their mission. This not only leaves less time for transition-related activities ahead of the September 2022 milestone, but it will also increase the potential that agencies may be “stuck” waiting for disconnect and transition services to be rendered. In particular, agencies that delay their EIS contractor selection for replacement services may find themselves “in line” behind those that have already chosen a contractor and made transition progress. This further slows progress for disconnecting services from the expiring contracts and connecting new services.
The extended contracts expire on May 31, 2023 and there will be no extensions. We invite our agency partners to ask themselves “Will we complete transition on time?”. If your agency will not complete transition on time, contingency planning must start now.
The time for EIS transition action is now. Regardless if your agency is in the acquisition or implementation phase, know that GSA wants to actively support agency transitions. If your agency is struggling, GSA can provide services such as:
- An inventory of complete services that need to be transitioned, including custom reports for your agency
- Technical, acquisition, and ordering assistance, plus automated tools to directly assist agencies with expediting EIS task orders
- GSA in-scope reviews of agency solicitations
- Regular outreach to agencies’ Integrated Transition Teams to monitor transition progress and provide guidance
If your agency needs help with transition, please contact the IT Customer Service Center at 855-482-4348, or send an email to ITCSC@gsa.gov. We encourage you to reach out to your agency leadership. Include Chief Information, Acquisition, and Financial Officers in conversations on EIS transition, financials, and risk.